Access rights control system
Use Access matrix, to start managing online employee access - Control rights, roles and access levels in one system.
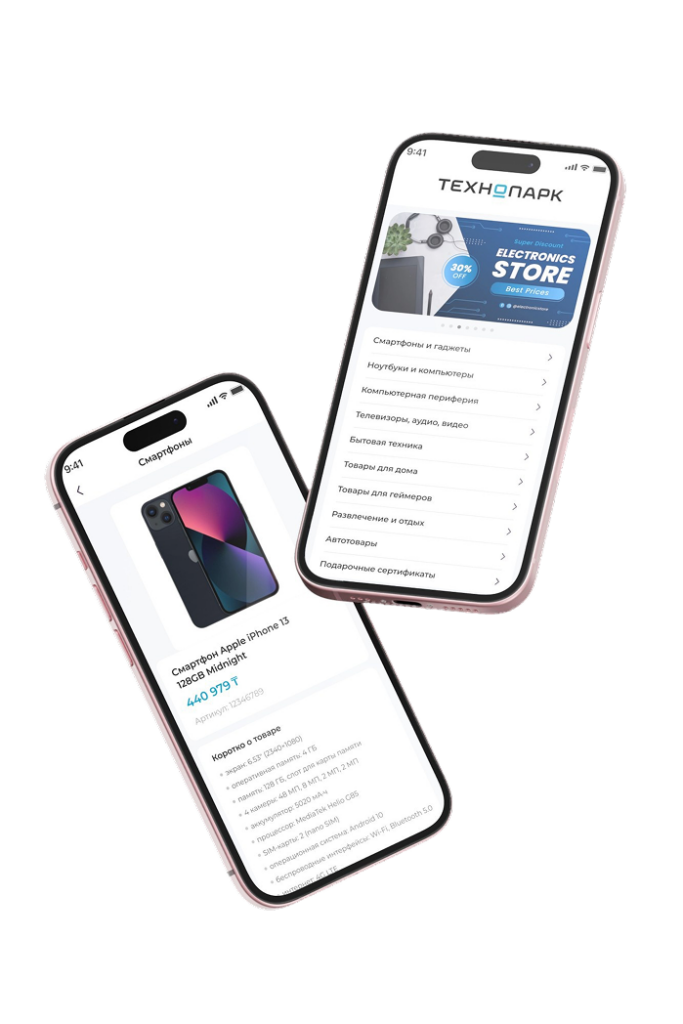
Intuitive interface for employees, approvers and administrators.
Submissions, approvals and access control are just a few clicks away.
Unified system for managing access to documents and IT assets
(information systems, databases, file resources).
Support for scaling and extending functionality.
The system works without interfering with business processes and does not disrupt existing IS.
Integration is performed without changing the logic of systems operation.
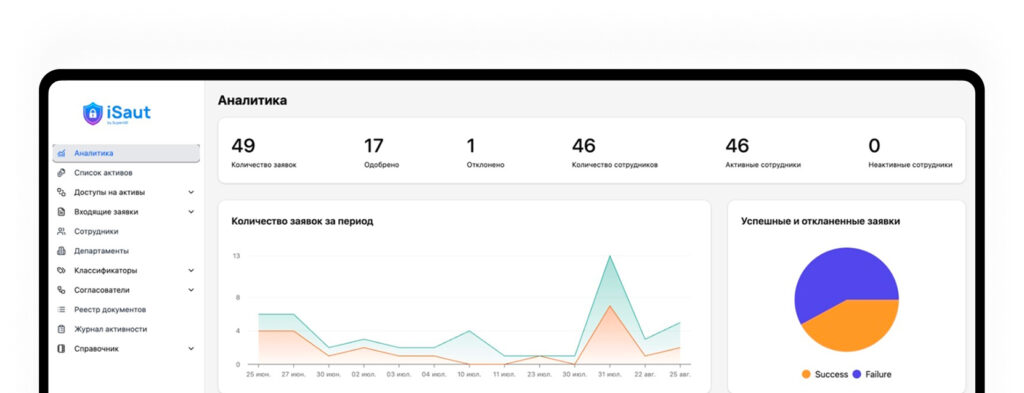
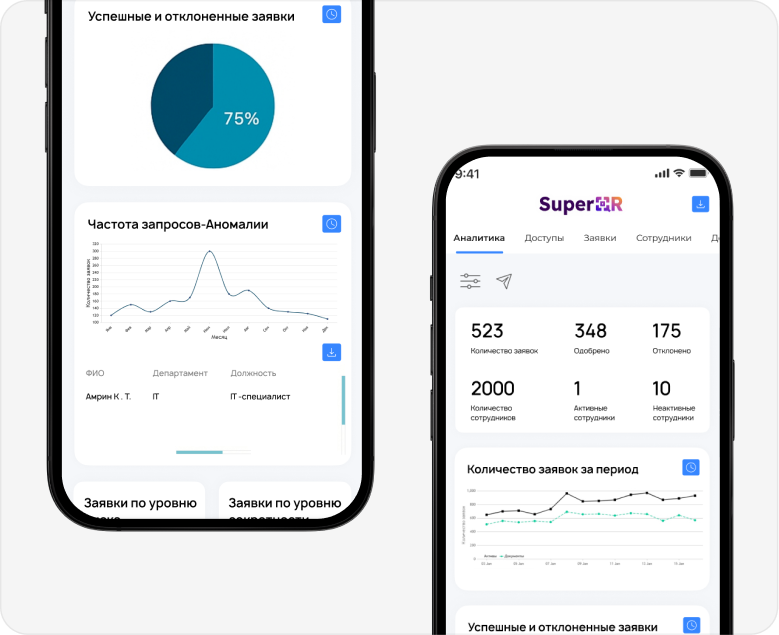
Allows you to see who, when, and what was accessed during any selected time period.
Handy for inspections, audits and incident investigations.
Displays accesses at the employee level rather than individual accounts.
Provides transparency and insight into the actual rights of each user.